Exploring the realm of Cloud vs. Local Hosting: Pros & Cons for Security, this piece delves into the nuances of security measures in the digital landscape, offering a comprehensive guide to navigating the complexities of hosting choices.
As we unravel the layers of security concerns and benefits associated with cloud versus local hosting, a deeper understanding emerges, shedding light on the crucial aspects that shape data protection strategies.
Cloud Hosting Security
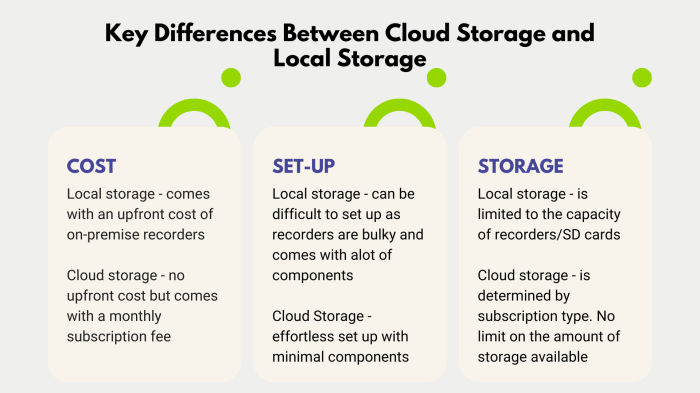
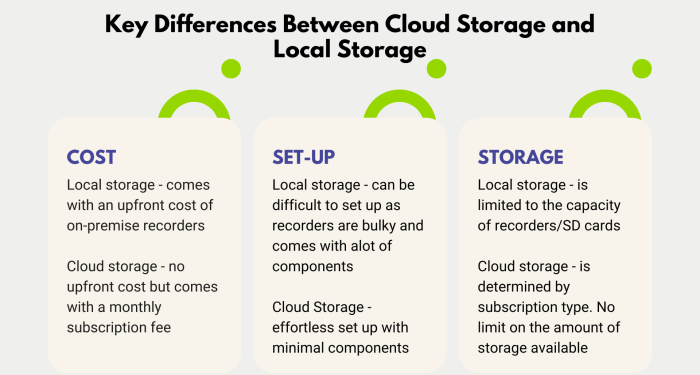
Cloud hosting security is a critical aspect of ensuring the protection of data and sensitive information in the digital landscape. Here, we delve into the security measures, risks, and advantages associated with cloud hosting, as well as the role of encryption in enhancing security.
Security Measures in Cloud Hosting
- Encryption: Data stored in cloud hosting is often encrypted to protect it from unauthorized access. Encryption algorithms scramble the data, making it unreadable without the decryption key.
- Firewalls: Cloud hosting providers implement firewalls to monitor and control incoming and outgoing network traffic, thus preventing potential security threats.
- Multi-factor authentication: Users are required to provide multiple forms of verification, such as passwords and biometric data, to access their cloud accounts, adding an extra layer of security.
- Regular security audits: Cloud hosting providers conduct frequent security audits to identify and address vulnerabilities in their systems, ensuring continuous protection.
Comparison of Security Risks
- Cloud Hosting: While cloud hosting offers robust security measures, there is still a risk of data breaches due to factors such as shared infrastructure and potential vulnerabilities in the cloud provider’s systems.
- Local Hosting: Local hosting may have lower risks of external attacks since data is stored on-premises, but it is also susceptible to physical threats like theft or damage.
Advantages of Cloud Hosting for Security
- Scalability: Cloud hosting allows for easy scalability of security measures as businesses grow, ensuring that security remains effective and adaptive to changing needs.
- Redundancy: Cloud hosting providers often have redundant systems and backups in place to prevent data loss in case of a security breach or system failure.
- Expertise: Cloud hosting providers specialize in security and have dedicated teams focused on monitoring, detecting, and responding to security threats, offering a higher level of expertise than many local hosting setups.
Role of Encryption in Cloud Hosting
- Encryption plays a crucial role in cloud hosting by securing data both at rest and in transit. Data encryption ensures that even if unauthorized access occurs, the information remains protected and unreadable without the encryption key.
- End-to-end encryption is commonly used in cloud hosting services to safeguard data throughout its entire journey, from the user’s device to the cloud server and back, ensuring comprehensive protection against interception or tampering.
Local Hosting Security
Local hosting environments also come with their own set of security protocols to safeguard data and prevent unauthorized access. While cloud hosting offers certain security advantages, local hosting provides a different level of control and protection over sensitive information.When it comes to security in local hosting environments, there are several key protocols typically implemented to ensure the safety of data:
Security Protocols in Local Hosting
- Firewalls: Firewalls are used to monitor and control incoming and outgoing network traffic, helping to prevent unauthorized access to the system.
- Encryption: Data encryption is utilized to encode information in a way that only authorized users can access it, adding an extra layer of security.
- Access Control: Access control mechanisms are put in place to restrict who can access certain data or systems, reducing the risk of breaches.
Despite these security measures, local hosting setups also have their vulnerabilities that can be exploited by malicious actors. Some potential weaknesses include:
Potential Vulnerabilities of Local Hosting
- Lack of Redundancy: Local hosting may lack the redundancy and backup systems that cloud hosting offers, making data more vulnerable to loss or corruption in case of hardware failure.
- Physical Security Risks: Local servers are susceptible to physical threats such as theft, natural disasters, or power outages, which could compromise data security.
- Patch Management: Without proper patch management, local hosting environments may be at risk of security vulnerabilities from outdated software.
In terms of security breaches, local hosting setups are not immune to cyber attacks and data breaches. Common examples of security breaches in local hosting include:
Common Security Breaches in Local Hosting
- Data Theft: Hackers may steal sensitive information stored on local servers, such as customer data or intellectual property.
- Ransomware Attacks: Local hosting systems can be targeted by ransomware attacks, where hackers encrypt data and demand payment for its release.
- Insider Threats: Employees with access to local servers may misuse their privileges to steal data or sabotage systems.
Despite these risks, having physical control over data in local hosting environments does offer some benefits for security purposes. Organizations can directly monitor and secure their servers, implement customized security measures, and ensure compliance with specific regulatory requirements.
Data Privacy and Compliance
Data privacy and compliance play a crucial role in the security of hosting solutions, whether it be cloud or local hosting. In this section, we will delve into how data privacy regulations impact security in cloud hosting, the challenges of ensuring compliance with data protection laws in local hosting, the ease of data privacy management between cloud and local hosting, and how data residency requirements influence security decisions in hosting choices.
Impact of Data Privacy Regulations in Cloud Hosting
- Cloud hosting providers are subject to various data privacy regulations such as GDPR, HIPAA, and CCPA, depending on the regions they operate in.
- These regulations require cloud hosting providers to implement stringent security measures to protect sensitive data, including encryption, access controls, and regular security audits.
- Non-compliance with data privacy regulations can lead to severe penalties, fines, and reputational damage for both the cloud hosting provider and their clients.
- Customers must ensure that their cloud hosting provider is compliant with relevant data privacy laws to safeguard their data effectively.
Challenges of Ensuring Compliance in Local Hosting
- Local hosting poses challenges in ensuring compliance with data protection laws due to limited resources and expertise compared to large cloud hosting providers.
- Organizations hosting data locally must invest in robust security measures, compliance frameworks, and regular audits to meet data privacy regulations.
- The responsibility of compliance falls entirely on the organization when hosting data locally, making it crucial to stay updated with evolving data protection laws.
- Non-compliance in local hosting can result in legal consequences, financial losses, and damage to the organization’s reputation.
Ease of Data Privacy Management in Cloud vs. Local Hosting
- Cloud hosting offers a more straightforward approach to data privacy management as providers typically offer built-in security features, compliance certifications, and dedicated teams to handle data protection.
- Local hosting requires organizations to take full responsibility for data privacy management, including implementing security protocols, training staff, and ensuring compliance with regulations.
- Cloud hosting can provide a more streamlined process for data privacy management, especially for organizations with limited resources or expertise in cybersecurity.
- Organizations must weigh the convenience of cloud hosting against the control and customization offered by local hosting when it comes to data privacy management.
Influence of Data Residency Requirements in Hosting Choices
- Data residency requirements dictate where data must be stored and processed, impacting the choice between cloud and local hosting based on legal and regulatory obligations.
- Certain industries or regions may have strict data residency laws that require data to be stored within specific geographic boundaries, influencing hosting decisions.
- Cloud hosting providers often offer data centers in multiple locations to comply with data residency requirements and provide flexibility to clients with varying compliance needs.
- Data residency plays a significant role in security decisions, as non-compliance can result in penalties, data breaches, and legal consequences for organizations.
Disaster Recovery and Backup
Disaster recovery and backup are critical components of maintaining security in both cloud and local hosting environments. In this section, we will explore the disaster recovery options available in cloud hosting, detail the backup mechanisms provided by cloud hosting services, compare the efficiency of disaster recovery strategies between cloud and local hosting, and discuss the importance of regular backups in maintaining security for both hosting options.
Disaster Recovery in Cloud Hosting
- Cloud hosting offers various disaster recovery options such as data replication across multiple servers in different geographical locations.
- Automatic failover mechanisms ensure that if one server fails, the workload is seamlessly transferred to another server to prevent downtime.
- Cloud providers often have redundant infrastructure and backup systems in place to protect against data loss in the event of a disaster.
Backup Mechanisms in Cloud Hosting
- Cloud hosting services typically offer automated backup solutions that regularly back up data to secure storage locations.
- Users can customize backup schedules and retention policies to meet their specific security and compliance requirements.
- Cloud backups are often encrypted to ensure the security and privacy of sensitive data.
Efficiency Comparison Between Cloud and Local Hosting
- Cloud hosting generally provides faster and more reliable disaster recovery options compared to local hosting.
- Local hosting may require manual intervention for disaster recovery, making it slower and more prone to errors.
- Cloud hosting’s scalability and redundancy make it a more efficient choice for disaster recovery and backup processes.
Importance of Regular Backups
- Regular backups are essential for both cloud and local hosting to prevent data loss in case of cyberattacks, hardware failures, or natural disasters.
- Backing up data ensures that critical information can be restored quickly to minimize downtime and maintain business continuity.
- Compliance regulations often require organizations to have backup and disaster recovery plans in place to protect sensitive data.
Closure
In conclusion, the comparison between Cloud vs. Local Hosting: Pros & Cons for Security unveils a multifaceted landscape of security considerations, urging individuals and businesses alike to contemplate the optimal hosting solutions that align with their security objectives and priorities.
User Queries
What are the main security risks associated with cloud hosting?
Cloud hosting risks include data breaches, account hijacking, and insecure APIs.
How does data privacy management differ between cloud and local hosting?
Cloud hosting offers centralized data privacy management, while local hosting requires individual data management on each server.



![5 Best eCommerce Marketing Digital Agencies [2024 Edition]](https://legal.goodstats.id/wp-content/uploads/2025/11/Best-E-Commerce-Marketing-Agencies-2048x1024-1-120x86.jpg)