How to Secure Client Data Using Digital Ocean sets the stage for this informative guide, providing an in-depth look at safeguarding client information in the digital realm. With a focus on practical strategies and solutions, this guide aims to equip readers with the knowledge needed to protect sensitive data effectively.
As we delve into the various aspects of client data security, readers will gain valuable insights on enhancing data protection measures and mitigating risks in an ever-evolving digital landscape.
Introduction to Client Data Security
Client data security is of paramount importance in digital environments to protect sensitive information from unauthorized access, theft, or misuse. Safeguarding client data not only ensures compliance with regulations but also builds trust with customers.
Inadequate client data protection poses significant risks to businesses, including financial losses, damage to reputation, and legal consequences. Data breaches can lead to severe repercussions, such as lawsuits, fines, and loss of customers’ trust.
Risks of Inadequate Client Data Protection
- Data breaches can result in financial losses due to theft of sensitive financial information like credit card details.
- Loss of customer trust and reputation damage can lead to a decrease in sales and potential long-term negative impacts on the business.
- Legal consequences, such as lawsuits and regulatory fines, can be incurred for failing to protect client data adequately.
Utilizing Digital Ocean for Client Data Security
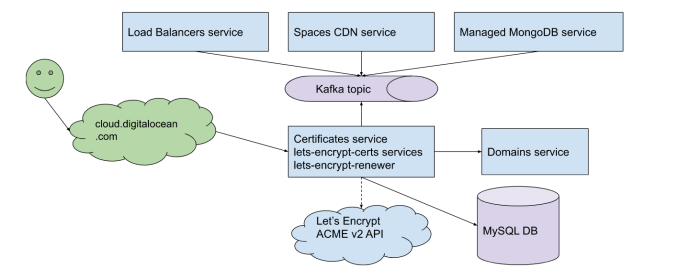
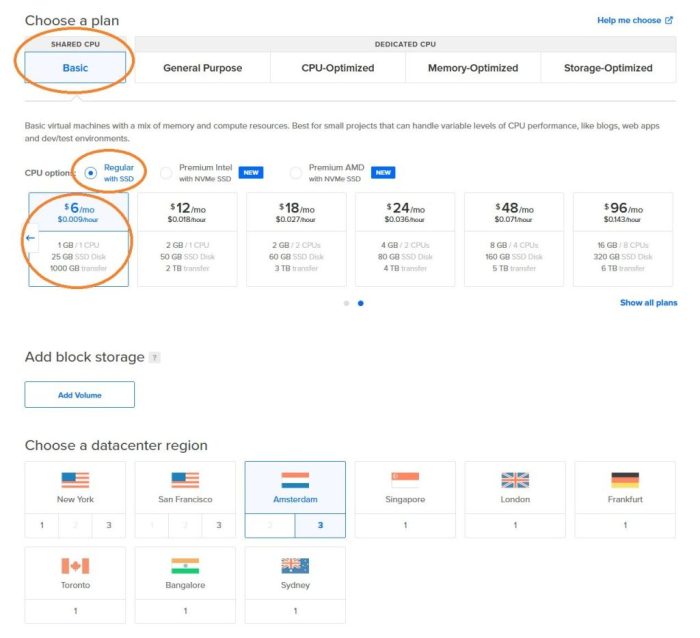
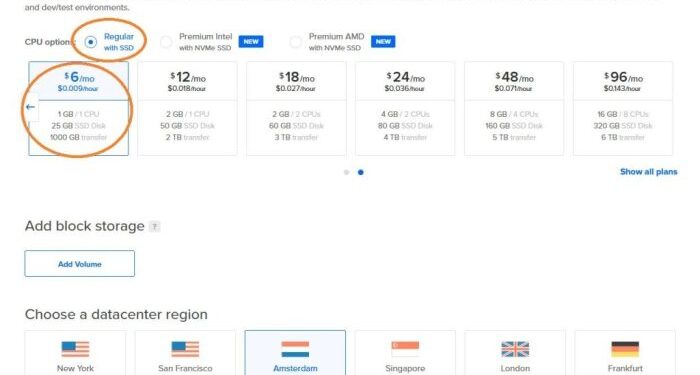
When it comes to securing client data, Digital Ocean offers a range of features that enhance data security and provide a secure environment for sensitive information.
Features of Digital Ocean for Data Security
- Virtual Private Cloud (VPC) – Digital Ocean allows users to create isolated virtual networks to secure their data and control access.
- Firewalls – Users can set up and configure firewalls to restrict access to their servers and protect against unauthorized access.
- Monitoring and Alerts – Digital Ocean provides monitoring tools to track server activity and set up alerts for any suspicious behavior.
- Data Encryption – Data stored on Digital Ocean servers can be encrypted to protect it from unauthorized access.
Comparison with Other Cloud Service Providers
Compared to other cloud service providers, Digital Ocean stands out in terms of data security measures. While all providers offer basic security features, Digital Ocean goes the extra mile by providing advanced tools and options for users to secure their data effectively.
Setting up a Secure Environment in Digital Ocean
- Create a Virtual Private Cloud (VPC) to isolate your resources and control network traffic.
- Set up firewalls to restrict access to your servers based on specific rules and configurations.
- Implement data encryption to protect sensitive information stored on Digital Ocean servers.
- Regularly monitor server activity and set up alerts for any unusual behavior that may indicate a security breach.
Implementing Encryption Techniques
Encryption plays a crucial role in securing client data by converting information into a code that can only be deciphered with the right key. This ensures that even if unauthorized parties access the data, they cannot understand or use it without the decryption key.
Types of Encryption Methods
- Symmetric Encryption: Involves using a single key to both encrypt and decrypt data. Examples include AES (Advanced Encryption Standard) and DES (Data Encryption Standard).
- Asymmetric Encryption: Uses a pair of keys – public and private – for encryption and decryption. RSA (Rivest-Shamir-Adleman) is a common example of asymmetric encryption.
- Hashing: While not encryption in the traditional sense, hashing algorithms like SHA-256 can secure data by generating a unique fixed-length string of characters from input data.
Tools for Data Encryption on Digital Ocean
- LUKS (Linux Unified Key Setup): A disk encryption tool that can be used to encrypt data on Digital Ocean servers at the disk level.
- Vault: A tool that provides encryption as a service, allowing you to encrypt sensitive data before storing it on Digital Ocean servers.
- TLS/SSL: Secure Sockets Layer/Transport Layer Security protocols that encrypt data transmitted between clients and servers, ensuring secure communication.
Access Control and User Permissions
Access control plays a crucial role in maintaining the security of client data. By implementing proper user permissions and access controls, organizations can ensure that only authorized individuals can view, modify, or delete sensitive information. This helps prevent unauthorized access and reduces the risk of data breaches.
Importance of Access Control
- Access control limits the exposure of client data to only those who need it for their job responsibilities.
- It helps organizations comply with data protection regulations and standards by ensuring data confidentiality and integrity.
- Proper access controls reduce the likelihood of insider threats and unauthorized access to sensitive information.
Best Practices for Managing User Permissions on Digital Ocean
- Utilize Digital Ocean’s Role-Based Access Control (RBAC) to assign specific roles and permissions to users based on their job functions.
- Regularly review and update user permissions to align with changes in roles or responsibilities within the organization.
- Implement multi-factor authentication (MFA) to add an extra layer of security to user accounts and prevent unauthorized access.
Strategies for Monitoring and Controlling Access to Sensitive Client Information
- Set up audit logs to track user activity and detect any unusual or unauthorized access attempts.
- Implement data encryption to protect client data both at rest and in transit, reducing the risk of unauthorized access.
- Regularly conduct security assessments and penetration testing to identify and address any vulnerabilities in the access control system.
Regular Data Backups and Disaster Recovery
Regular data backups and disaster recovery plans are essential components of client data security. By backing up data frequently, businesses can protect themselves from data loss due to various reasons such as hardware failure, cyber attacks, or accidental deletion. Additionally, having a disaster recovery plan in place ensures that businesses can quickly recover and resume operations if a data breach or loss occurs.
Setting up Automated Backups on Digital Ocean
Automated backups can streamline the process of data backup and ensure that important data is consistently backed up without manual intervention. On Digital Ocean, users can set up automated backups through the control panel. By enabling this feature, users can schedule regular backups of their server instances, databases, and files.
This not only saves time but also helps in maintaining the integrity and security of client data.
Importance of Disaster Recovery Plans
Disaster recovery plans are crucial for businesses to minimize downtime and mitigate the impact of data breaches or loss. These plans Artikel the steps to be taken in case of a data disaster, including data recovery procedures, communication protocols, and system restoration processes.
By having a well-defined disaster recovery plan in place, businesses can ensure business continuity and safeguard client data in the event of a crisis.
Closing Notes
In conclusion, securing client data using Digital Ocean is not just a necessity but a strategic imperative for businesses operating in today’s interconnected world. By implementing the best practices Artikeld in this guide, organizations can fortify their defenses and ensure the confidentiality and integrity of client information.
Helpful Answers
What are the common risks associated with inadequate client data protection?
Inadequate client data protection can lead to unauthorized access, data breaches, identity theft, and reputational damage for businesses. It is crucial to prioritize robust security measures to mitigate these risks effectively.
How can I set up automated backups on Digital Ocean for client data security?
Setting up automated backups on Digital Ocean involves configuring snapshots or using backup services provided by the platform. By scheduling regular backups, businesses can ensure data availability and integrity in the event of unexpected data loss.
What role does encryption play in safeguarding client data?
Encryption is essential for protecting client data by converting information into a secure format that can only be accessed with the proper decryption key. Implementing encryption techniques adds an extra layer of security to prevent unauthorized access to sensitive information.



![5 Best eCommerce Marketing Digital Agencies [2024 Edition]](https://legal.goodstats.id/wp-content/uploads/2025/11/Best-E-Commerce-Marketing-Agencies-2048x1024-1-120x86.jpg)